If your email becomes a scam target, act fast by changing your password to a strong, unique one and enabling two-factor authentication. Review and update recovery options, avoid clicking suspicious links, and scan your device for malware. Monitor your accounts for unusual activity, report scams to your provider, and stay alert for phishing attempts. Staying proactive and vigilant is key—keep going to discover more essential tips to protect yourself and your information.
Key Takeaways
- Change your email password immediately to a strong, unique combination and enable two-factor authentication.
- Review and update recovery options, and monitor account activity for suspicious behavior.
- Run antivirus scans and keep software updated to detect and prevent malware or unauthorized access.
- Notify your contacts about the scam to prevent further spread and avoid sharing sensitive information.
- Report the incident to your email provider and relevant authorities for assistance and investigation.

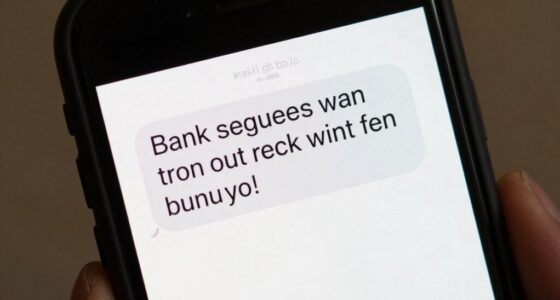
If your email address has become a target for scammers, it’s vital to act quickly to protect your personal information and prevent further damage. Scammers often use your email to carry out phishing prevention tactics, aiming to trick you into revealing sensitive details or installing malicious software. The first step is to change your password immediately. Choose a strong, unique password that combines upper and lowercase letters, numbers, and symbols. Avoid reusing passwords from other accounts, as this can make it easier for hackers to gain access to multiple platforms if one gets compromised.
Act quickly to change your password and secure your email from scammers and phishing attacks.
Next, review your account recovery options. Update your security questions and backup email addresses to guarantee only you have access to reset your account if needed. Enable two-factor authentication (2FA) wherever possible. This adds an extra layer of security, requiring a second verification step before granting access. It’s a vital measure in phishing prevention, making it harder for scammers to hijack your account even if they obtain your password. Regularly checking your account activity helps identify suspicious behavior early on, especially if you monitor for unusual login attempts. Being aware of common cybersecurity threats can further help you recognize warning signs early. Additionally, staying informed about new scam tactics can help you identify potential threats before they cause harm.
Be cautious about any suspicious emails you’ve received or sent recently. Look out for signs of phishing attempts, such as urgent language, unfamiliar sender addresses, or links that don’t match legitimate websites. Don’t click on any links or download attachments from unknown sources. Instead, verify the sender’s identity directly through official channels. If you notice any unauthorized activity or suspect your account has been compromised, report it immediately to your email provider’s support team.
You should also run a thorough scan on your device using reputable antivirus software. Phishing attempts are often accompanied by malware or spyware that can further jeopardize your security. Removing any malicious software helps prevent identity theft and limits the damage scammers can do. Keeping your operating system and all applications up to date is essential, as updates often include security patches that defend against new threats. Regularly updating software is a crucial step in maintaining your digital security.
Finally, monitor your financial accounts and credit reports for any signs of identity theft. If you notice unfamiliar transactions or accounts, report them promptly. Consider placing a fraud alert or credit freeze to prevent scammers from opening new accounts in your name. Staying vigilant and proactive is essential in minimizing the impact of a scam targeting your email address. Remember, quick action combined with good cybersecurity habits is your best defense against scammers and identity theft. Additionally, understanding accessibility features can help you better protect yourself and manage your online security more effectively.

Strong password generator
Set up a complex password
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Can I Prevent My Email From Being Targeted in the First Place?
To prevent your email from being targeted, you should practice strong password management by creating unique, complex passwords for each account. Stay vigilant with phishing awareness, avoiding suspicious links or attachments. Enable two-factor authentication whenever possible, and regularly update your security settings. Keep your software current, and don’t share your email credentials. These habits considerably reduce your risk of falling victim to email scams.
Are There Specific Signs Indicating My Email Has Been Compromised?
Your email might be a target if you notice scam indicators like unexpected login alerts, strange emails in your sent folder, or messages asking for personal info. It’s like catching a whiff of smoke before a fire; phishing techniques often leave subtle clues. Stay alert for unusual activity, such as password changes or unfamiliar contacts, and act quickly to secure your account before it’s fully compromised.
Should I Change My Email Address Immediately After a Scam Attempt?
Yes, you should change your email address immediately after a scam attempt. This helps protect your accounts and personal info from further phishing attacks. Enhance your security by enabling email encryption and practicing phishing awareness. Make sure to update your login details across services, and inform trusted contacts about the new email. Staying vigilant and adopting these measures reduces the risk of future scams and keeps your digital identity safe.
What Are the Long-Term Consequences of Email Scams?
Email scams can lead to long-term consequences like compromised personal information, financial loss, or damaged reputation. If you fall victim, scammers can misuse your data for future phishing awareness attacks or identity theft, impacting your trustworthiness. These scam repercussions may require ongoing monitoring and security measures. Staying vigilant and educated about scam tactics helps prevent lasting damage, but recovery can be complex and time-consuming.
Can I Recover a Hacked Email Account Easily?
You can recover a hacked email account, but it requires quick action. Start with password recovery options offered by your provider and verify your identity through account verification steps. Change your password to a strong, unique one, and enable two-factor authentication for added security. Keep an eye on your account activity and update your recovery information to prevent future hacking attempts. Recovery is possible if you act promptly and follow these steps.

Thetis Pro FIDO2 Security Key, Two Factor Authentication NFC Security Key FIDO 2.0, Dual USB A Ports & Type C for Multi layered Protection (HOTP) in Windows/MacOS/Linux, Gmail, Facebook,Dropbox,Github
Check FIDO2 compatibility before purchase – Known limitations: ID Austria is not supported (requires FIDO2 Level 2). Windows…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
Think of your email as a sturdy lighthouse amidst turbulent waters. When scammers target it, you’re guiding your own beacon back to safety, shining a clear light on the deception. Protect your signal by changing passwords and staying vigilant, ensuring your light remains steady and bright. Remember, even in stormy seas, your awareness keeps you afloat, steering you away from hidden rocks. Keep your lighthouse strong—your digital safety depends on it.

McAfee Total Protection 5-Device | AntiVirus Software 2026 for Windows PC & Mac, AI Scam Detection, VPN, Password Manager, Identity Monitoring | 1-Year Subscription with Auto-Renewal | Download
DEVICE SECURITY – Award-winning McAfee antivirus, real-time threat protection, protects your data, phones, laptops, and tablets
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Internet Password Organizer: Website, Username, Password, Email and Notes Logbook – Keep Record of your Cyber Credentials on the Go!
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.